As soon as the world went into lockdown, digital transformation became a top priority. Many organisations saw two years of transformation initiatives carried out in as little as two months. This rapid adoption of digital technologies enabled businesses and governments to keep the show running and helped cushion economies worldwide. But through this period of rapid change, organisations have become more vulnerable to cyber threats. Adversaries feed on uncertainty, and the sudden transition to new ways of working provided them with the perfect opportunity. Many countries witnessed a steep rise in cyber breaches, and security has become a hot topic in management circles. The digital technologies are not to blame, but the lack of a security framework around them is. Customers often ask about how Riverbed approaches cybersecurity, so let’s take a deeper look at a real-world example.
How Riverbed is helping government organisations become more secure
The Australian Cyber Security Centre’s (ACSC) prescribed Essential Eight has laid out a clear game plan for security for government organisations. ACSC’s Essential Eight is a series of baseline mitigation strategies from the ‘Strategies to Mitigate Cyber Security Incidents’ recommended for organisations. Implementing these strategies as a minimum makes it much harder for adversaries to compromise systems. Mapping their activities to Essential Eight framework provides them with a path to level up their security and address ongoing upgrade requirements.
Government agencies across Australia have been mandated to comply with the Essential Eight sooner rather than later. But mandates aside, the Essential Eight goes a long way towards improving your cybersecurity posture. The layer of security tools won’t hamper your ongoing processes, but it will act as a shield that protects you and your communities against adversaries. Compliance will ensure sustainability, protect your credibility, and elevate your role as a government agency.
Three key aims underpin the Essential Eight:
- Enhance resilience against cyber attacks
- Increase in customer trust
- Maintain data sovereignty
It’s important to realise that maintaining security is an ongoing process. We are working closely with several government agencies and helping them implement key network technologies so they can provide uninterrupted services to Australian citizens safely and reliably. One notable project I personally worked on was for a large government agency in NSW.
As the first step to compliance with the Essential Eight, we began investigating devices in their existing network and ensuring we tied up loose ends while keeping the end-user experience intact. When we say loose ends, there are a lot of different possibilities. For example, in the case of this government agency, some of the issues we found included:
- Unauthorised applications installed on some devices
- Some devices running older versions of some applications
- Users not cleared for admin-level access had full access anyway, allowing them to install unauthorised applications freely
Clearly, they needed a deeper dive into their network and security systems and a solution that could give them whole-of-network visibility. Riverbed Aternity suite was the perfect fit for the job. The benefits of implementing Aternity are manifold, so let me walk you through the specific issues we resolved by using it.
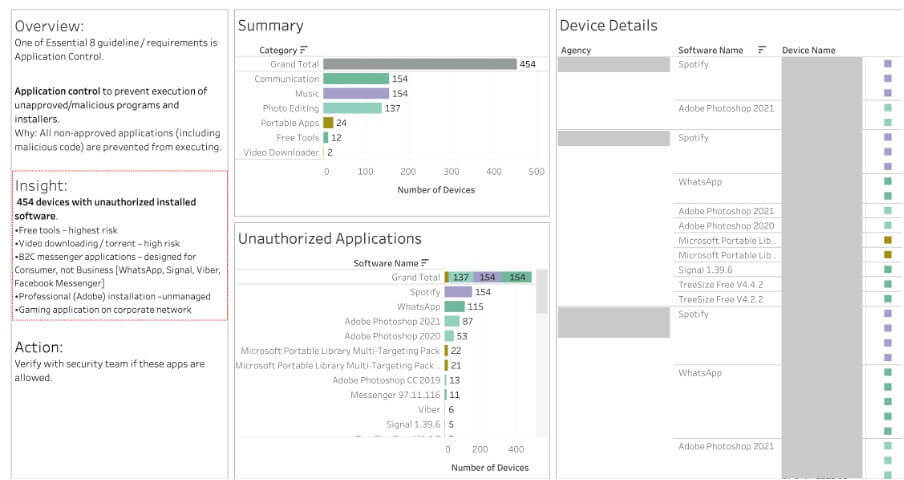
Implementing application controls
We began by implementing the Essential Eight mitigation strategy, and the first step for this was Application Control. Aternity helped identify 454 devices out of 20,000 we scanned with unauthorised software installed. We quickly remediated this risk by uninstalling unauthorised applications.
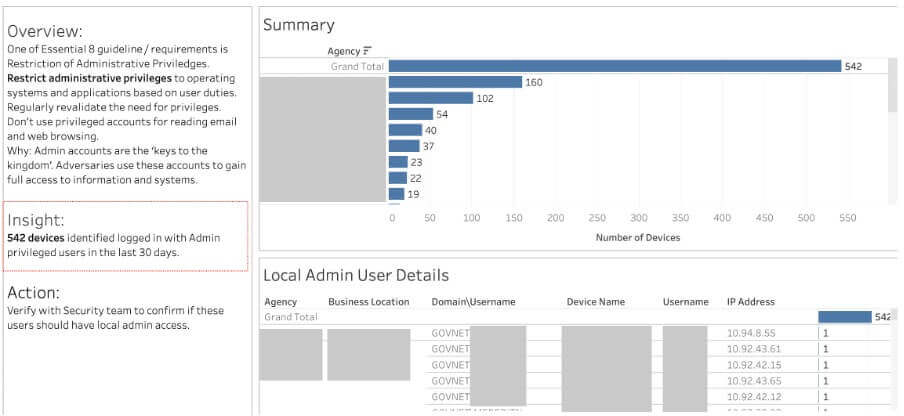
Restricting admin access
The next task was to restrict admin access. Aternity identified 542 unauthorised user devices that were granted admin access. This revelation was shocking for the government agency, as it was like having the keys to the kingdom out in the wild. Users were granted permanent access when they requested admin access to install a particular software for work purposes. Once this issue was identified, they revoked the access of unauthorised users and started granting only temporary access to verified users.
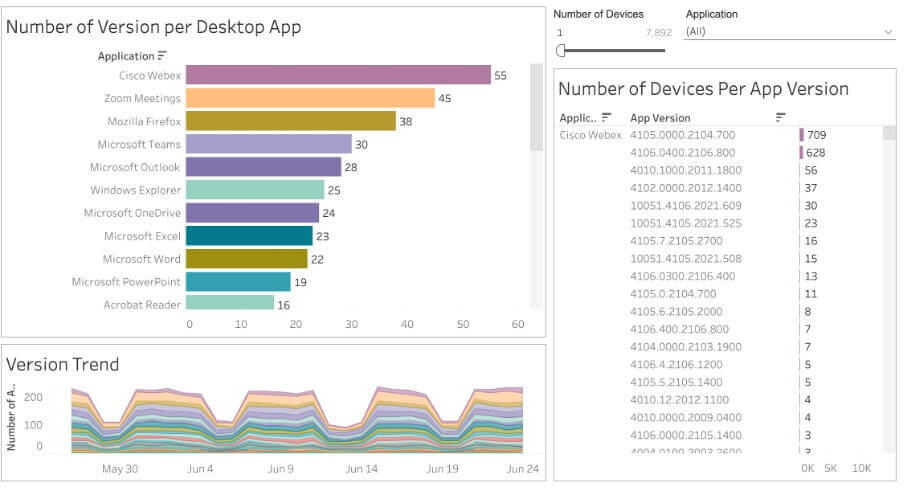
Patching applications and the OS
Essential Eight also prescribes using the latest version of applications and installing patches as and when available. While most of the devices on their network were using up-to-date applications, a few were still not using the latest versions. We found 55 versions of Webex, 45 versions of Zoom and 38 versions of Firefox on some of the machines, which was a considerable security risk.
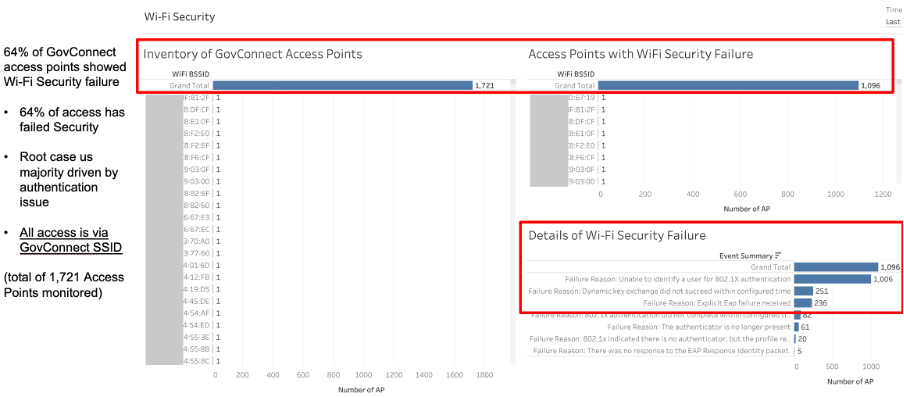
Strengthening Wi-Fi security
When Aternity scanned all the endpoints, it reported security failure across 64% of wi-fi access points (1,721 access points in total). Aternity monitors all endpoints and can also show where users were accessing the internet from. Some of them were using unsecured wi-fi at cafes, libraries or hotels. When users connected to the agency SSID, we found many devices failed the wi-fi security check. Based on our analysis, this problem was dominant in certain areas, so we could identify specific users and help them mitigate this issue.
Updating AV check status
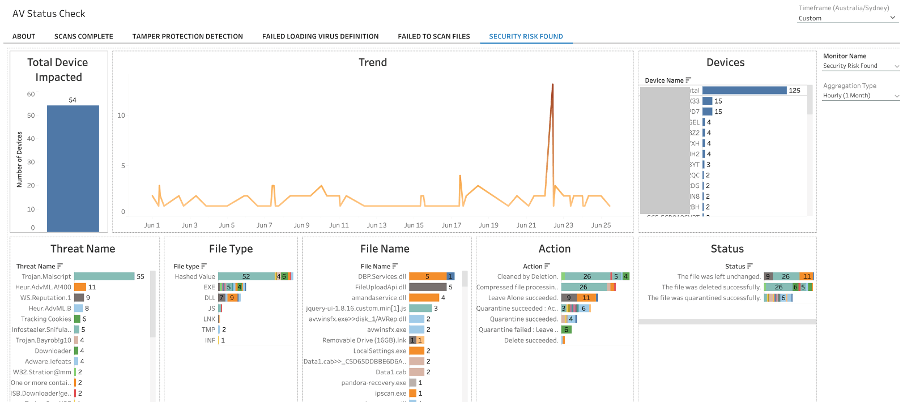
Aternity monitors all agents, including security agents, on each machine in the network for our client. We completed over 52,788 AV scans in 14 days. On further analysing the results of the status checks, we quickly identified security threats from 54 devices detected by Symantec. 44% of the threats are because of “Trojan.Malscript”.
Implementing proactive monitoring
Proactive monitoring enables anomaly detection and automated alerts. We also integrated Aternity with ServiceNow for this client. When Aternity detects anomalies, it automatically creates a ticket in ServiceNow, and the issue is fixed as per standard SLAs to minimise the impact on users.
With Riverbed Aternity, finding loose ends, fixing them, ensuring Essential Eight compliance, and improving customer experience became effortless. We have laid a secure foundation for their network and user devices. Now, they can monitor security threats, mitigate them on an ongoing basis, and follow up on other Essential Eight prescribed best practices to maintain their security posture. With Riverbed Aternity by their side, they are well-equipped for the challenge.
Have you reviewed the risks to your organisation?
A survey of Australian businesses showed that 76% were victims of cyber-attacks due to a lack of cyber preparedness in 2021. The Australian Cyber Security Centre (ACSC) recorded a 13% increase in reports of cyber threats, which comes to over 67,000+ complaints. However, when I meet with clients, it is reassuring that most senior executives and government agencies realise the need for a comprehensive security program that touches all aspects of the organisation.
Essential Eight compliance gives your end customers the confidence that their data is safe and in responsible hands. The rewards make it well worth the investment. Whatever be your organisation’s landscape, Riverbed Aternity fits well into every network type and delivers on your unique cybersecurity needs. Having a trusted cyber security partner can go a long way in securing your network. Speak with us today to explore how Riverbed Aternity can help your organisation.
