When a high-profile hack or malware campaign hits the news, everyone’s first question is, “How do I know if I’m affected?” Security analyses and official guidance frequently contain indicators of compromise, but they rarely explain how to make use of them. Network visibility tools such as Riverbed NetProfiler and AppResponse can form an important part of any enterprise’s plan to scour its infrastructure for signs of compromise. This post references a recent, widely-reported cyberattack, SUNBURST, to illustrate how to use Riverbed NPM solutions to find and root out malicious actors based on common indicators of compromise.
Malware and similar malicious software must often use the network in executing a cyberattack, which may include communicating with Command and Control (C2) servers, downloading malicious payloads, uploading stolen data or spreading through the network. Oftentimes, these actions are designed to appear innocuous, but can still be identified as suspicious through indicators such as domain names, IP addresses, file names or unique ports. Enterprises can use these indicators to search their networks for malicious activity.
In December 2020, cybersecurity firm FireEye released an investigation of a global network intrusion campaign where hackers managed to insert a vulnerability within certain SolarWinds® Orion® Platform software builds and software updates released between March and June 2020. The Cybersecurity and Infrastructure Security Agency (CISA) followed suit with its own analysis and advisory. This cyberattack, also known as SUNBURST, has had pervasive reach due to its roots in the compromised vendor supply chain. Investigations published so far have included several indicators of compromise that are potentially of use.
Riverbed NetProfiler: long history, global reach
One of the biggest challenges in detecting compromises is that by the time the details and behavior of malware are known, it may have been weeks or months since that malware first started circulating. This is why flow tools, like Riverbed NetProfiler, are indispensable in looking for malware: it is possible to search historical network flow data for even small connections that would otherwise fly under the radar. In order to scale well, flow records must be sparse, but they contain IP addresses and ports and show how hosts connect to each other.
FireEye identified a number of IP addresses of forensic interest in relation to the SUNBURST cyberattack. NetProfiler customers can easily search for these hosts by scanning historical flow data. In the excerpt below traffic expression is merely built up from one or more host names:
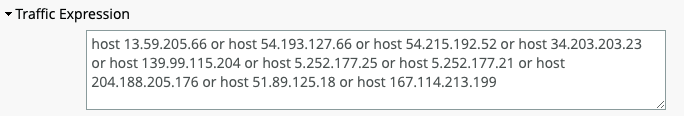
Very often, further analysis turns up new IP addresses—either because new features of the malware have been discovered, or because the attackers have made changes to their infrastructure in response to news coverage. Using NetProfiler, it is easy to adjust the filter and check again, looking at as much history as possible.
Another indicator to watch for is the malicious use of cloud services. In the excerpt above, the first host listed is in Amazon AWS. Threat actors may use public services so that their IP addresses look more innocuous and their use of such public services tends to be short-lived. It is important to look for these indicators, keeping in mind that communications with public service hosts could be another service reusing the same IP. Time frame is key to understanding the risk, and malware analyses frequently include discussions about the times in which that malware was active: With respect to SUNBURST, FireEye’s countermeasures list includes a “First Seen” and “Last Seen” time frame ranging from February to December 2020.
Visualize the attack
NetProfiler’s ability to visualize patterns of connections over time is another key feature that can be used to better understand cybersecurity threats. In a typical forensic investigation, changing patterns of network behavior analysis would be used once a host has been identified as having been potentially compromised—for example, after seeing a suspicious communication to a C2 server. In the example below, however, it is a particular appliance that has been compromised.
Using Riverbed NetProfiler, customers can filter communications involving the IP of the appliance in question, and then use the network graph to examine the connections the appliance makes within the customer’s network. Unusual external connections may represent new indicators of compromise or other assets belonging to the cyber-attacker. Unusual connections within the network may indicate behaviors such as reconnaissance, lateral movement or attempts to initiate secondary compromise.
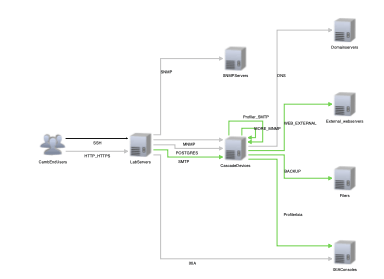
Each suspicious connection illuminates a potential move within the network by the threat actor. Duration, size, and type can shed light on what purpose a connection might serve. Context, in the form of patterns displayed before infection, can help weed out ordinary connections and expose unusual ones. The availability of historical data in Riverbed NetProfiler means that customers never have to wonder if a pattern is usual or not: just go back further in the historical record to see.
Riverbed AppResponse: the truth is in the packets
For ground truth in network investigations, nothing beats actual copies of the packets being sent. There are many packets to trawl through, however, and so packets require forethought to make use of them. Alerts can be set up based on suspicious transactions with considerably more depth than is available in flow records. Capture jobs can be created to have full access to potentially malicious traffic.
Reading through technical descriptions of malware behavior can yield useful results. These analyses frequently uncover useful indicators, in particular: first, the domain names used by adversaries, and second, packet captures of the communications themselves.
Leveraging DNS in your security search
The domain names can be useful in a number of ways. In the case of the SUNBURST cyberattack, a particular domain name, avsvmcloud[.]com, was identified as important to the attack progression. First, of course, Riverbed AppResponse customers can look up what IP addresses it currently and previously resolved to and search for those IP addresses in past and ongoing traffic. Riverbed Packet Analyzer Plus customers have the additional option of starting a capture job on UDP port 53 to examine DNS queries. Looking to see who is requesting DNS resolution of malicious domains in this way can be a powerful tool for quickly identifying affected hosts.
It is important when examining domain names to understand some of the ways adversaries use them. FireEye identified some sandbox-detection behavior in the SUNBURST cyberattack, in which the malware generated domains in a loop and tried to resolve them to see if they resolved as local IP addresses (an indicator that the malware was in a monitored environment so that it could stop execution). While it might be possible to form a list of these names to watch for them, seeing randomized domain names in DNS requests is a red flag that is not always a feasible way to search for indications of a particular malware strain.
Just as web applications are enterprise-critical, they are critical to many malicious campaigns as well. HTTP is often used to transfer files, commands or other information. Although malicious actors can and do use custom or encrypted protocols, just as often, they use standard protocols for the same reasons that commercial developers do, including reliability and ease of development.
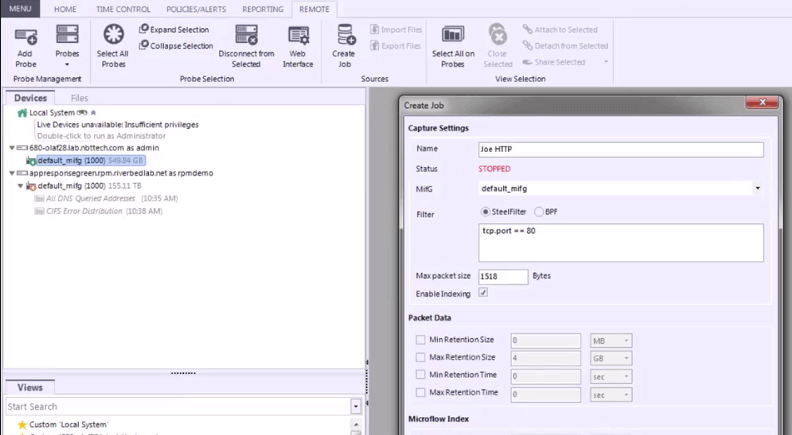
FireEye’s SUNBURST analysis provides several examples of the use of HTTP. For example, FireEye describes communication with C2 servers, including JSON payloads with a variety of fields. For example, the key “EventType” is hardcoded to “Orion” and “EventName” to “EventManager.” Riverbed AppResponse Web Transaction Analysis (WTA) module is very useful here. Just as Riverbed AppResponse customers can analyze business transactions, they can analyze the adversary’s transactions and search for indicative fields like these key/value pairs. Another analysis, by GuidePoint Security, identified a set of HTTP requests including “logoimagehandler.ashx” and query parameters such as “clazz” that indicate potential webshell communications.
AppResponse customers can also look for web transfers of files in the same way or web requests to malicious domains. Reading through the details of how malicious actors communicate will reveal what to watch for in their traffic.
Summary
While this post outlines indicators of network compromise specific to the SUNBURST cyberattack, the important lesson to learn here is not the indicators and security analytics tied to any one malware campaign. Instead, it is to learn how to read reports and analyses on malware to quickly identify key indicators that can be leveraged using the tools Riverbed NetProfiler and AppResponse customers already have. More specifically, IP addresses and domain names can be simple and reliable indicators of which network hosts to examine. Watch for key information such as the devices targeted and the time frames in which the malicious campaigns took place. And when in doubt, please reach out to Riverbed for help and advice.
