TLS certificates are the foundation of secure communication for modern networks, establishing trust between systems, enabling encryption, and verifying that users and services connect to the right endpoints. Because they are distributed across servers, load balancers, edge services, and security infrastructure, managing and tracking which certificates are in use for any given connection can quickly become complex.
That challenge becomes more pressing as certificate lifetimes get shorter. What was recently a 398-day cycle is now being reduced toward a 47-day maximum. Certificates that were reviewed periodically now require more frequent attention, increasing the likelihood of missed renewals, configuration drift, and more time spent troubleshooting when something breaks.
Most organizations already have tools to issue and renew certificates. The challenge isn’t lifecycle management. It’s confirming that certificate updates are applied correctly and do not introduce issues in production.
Why TLS Lifetimes Are Shrinking and What It Means for Operations
The move toward shorter TLS certificate lifetimes is being driven by the CA/Browser Forum and enforced by major browser vendors like Google, Apple, and Mozilla. The goal is to reduce risk.
| Date | Max Cert Validity | Domain Reuse |
| March 15, 2020 | 398 days | 398 days |
| March 15, 2026 | 200 days | 200 days |
| March 15, 2027 | 100 days | 100 days |
| March 15, 2029 | 47 days | 10 days |
Shorter lifetimes limit the window of exposure if a certificate or private key is compromised and reduces reliance on long-lived credentials that can drift out of compliance. Reduced lifetimes also push organizations toward more automation and consistent management practices.
The operational impact of these changes is straightforward: certificates are replaced more frequently, and validation windows are shrinking. As a result, the pace of change increases – certificates are updated more often and small inconsistencies surface more quickly.
When issues occur, teams still need to determine:
- Which certificate is in use
- Whether the correct certificate was presented
- If expected protocols and ciphers were negotiated
Logs and alerts can point to symptoms, but they rarely provide the context to resolve issues quickly. As certificate changes happen more often, that lack of context becomes harder to work around.
Where AppResponse Fits
As TLS certificate lifetimes move toward 47 days, teams are required to validate certificate changes far more frequently. The challenge isn’t just managing renewals. It’s confirming that those changes are working as expected in production.
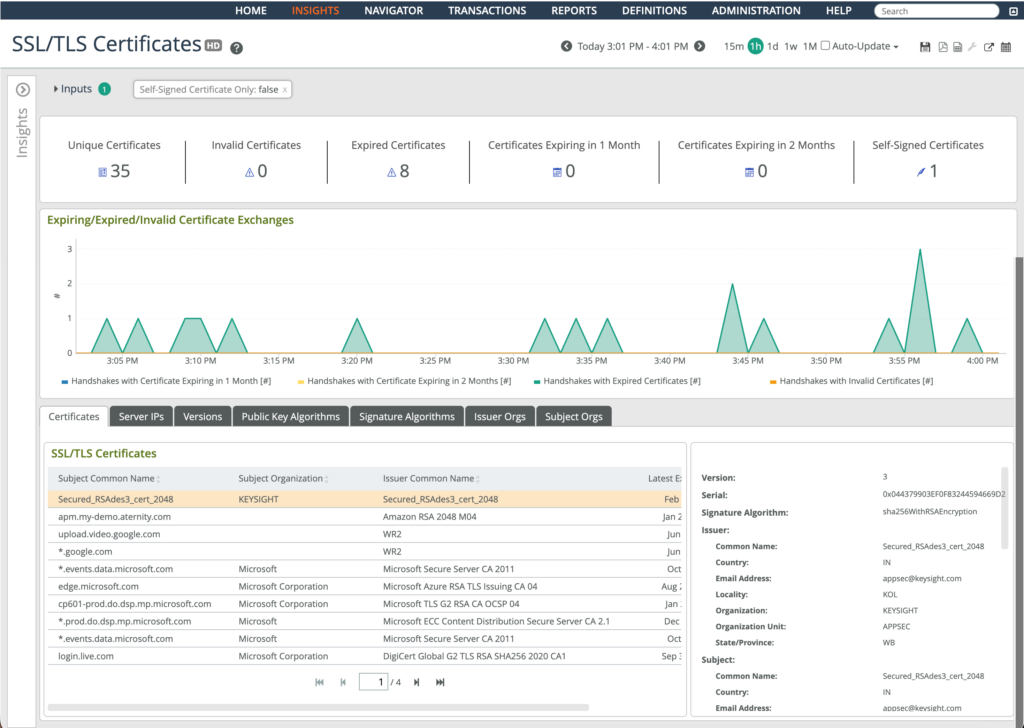
Riverbed AppResponse reduces the time required to verify certificate changes and troubleshoot issues by making certificate behavior visible in real traffic.
- Understand certificate usage in real traffic: AppResponse shows which certificates are actively in use and alerts when they approach expiration, helping teams focus on the certificates that affect production.
- Detect configuration drift from frequent updates: More frequent certificate rotation increases the likelihood of inconsistent configurations. AppResponse detects weak or non-approved ciphers and TLS versions before they cause outages or failed validations.
- Validate certificate deployments during TLS handshakes: AppResponse exposes handshake behavior in detail, allowing teams to confirm that newly deployed certificates are presented correctly.
- Identify trust chain issues introduced during certificate rotation: Frequent updates increase the chance of missing intermediates or misconfigured chains. Packet-level visibility allows teams to confirm the full certificate chain is presented correctly and pinpoint where validation breaks down.
These capabilities apply across on-prem, cloud, and hybrid environments, allowing teams to verify certificate changes and resolve issues quickly as certificate lifecycles accelerate.
Managing TLS at a Faster Pace
The shift to 47-day TLS certificates increases the frequency of change and reduces the tolerance for error. AppResponse provides the visibility teams need to confirm that certificate updates are working as expected and to identify issues quickly when they are not.
See How AppResponse Supports 47-Day TLS Certificate Lifecycles
To discover how AppResponse helps you monitor certificate expiration, validate certificate deployments, and identify issues introduced by more frequent certificate changes, visit Riverbed AppResponse.
